Just yesterday morning, hackers compromised the computer systems of a major contractor responsible for providing background checks for the U.S. government. (Source: CNN) And, in light of this week’s other enormous security breach by a Russian gang, first reported in The New York Times, we thought it was important for you to be able to explain to your clients and/or customers the value of migrating your website to HTTPS.
HTTPS (or HyperText Transfer Protocol with Secure Sockets) is designed to mask (or encrypt) order form data. The information traveling between your browser to the end retailer’s server is encrypted and decrypted en route.
What’s This Have To Do With SEO?
If you’ve heard or read the news about Google stating that secure websites (those with SSL encryption) will be given a “minor” ranking factor, I wouldn’t get too excited. Professional online marketers should be thinking of the security of their client’s online business and the safety of website visitors before jumping on the SEO bandwagon.
That’s not to say there aren’t guidelines to follow that will minimize a rankings disruption should you decide to move your clients’ sites from HTTP to HTTPS. In fact, a regular reader of this blog is conducting a test to determine if switching over to HTTPS from HTTP can be done smoothly rather than looking for the “rankings boost” that the search industry is yammering about.
Subscribe to our RSS feed to be notified when we publish his post.
Google outlines how to avoid common HTTPS pitfalls and provides guidance in showing visitors that your site is secure. Specifically,
- Redirect your users and search engines to the HTTPS page or resource with server-side 301 HTTP redirects.
- Use relative URLs for resources that reside on the same secure domain.
- For example,
Use<a href=”/about/ourCompany.php”> to refer to a page on your site
Rather than <a href=”https://example.com/about/ourCompany.php”>
Doing so ensures your links and resources always use HTTPS. It also has the side benefit of making local development less error prone because images, pages, and other resources are loaded from your local development environment instead of the production environment.
- Use protocol relative URLs for all other domains (e.g. //petstore.example.com/dogs/biscuits.php), or update your site links to link directly to the HTTPS resource.
- Use a Web server that supports HTTP Strict Transport Security (HSTS) and make sure it’s enabled.
This mechanism tells the browser to automatically request pages using HTTPS even when the user enters HTTP in the browser location bar. It also tells Google to serve secure URLs in the search results. All this minimizes the risk of serving unsecured content to your users.
If you’re worried about this throwing a wrench in your ability to track queries, the keyword data is stripped anyway. According to John Mueller, Google Webmaster Trends Analyst, the query is generally removed from the referrer regardless of whether the site uses HTTP or HTTPS. I guess we can consider Google to be “an equal opportunity [not] provider!”
Does Every Site Need to Switch to HTTPS?
If you’re running an online store, an e-commerce website or any site requiring a unique login, you should be aware of the vulnerabilities that exist even with a layer of encryption.
What consumers, businesses and website owners do not realize is that the encryption is only as secure as the host computer.
This is one reason why cyber security experts recommend two-step authentication and authorization for Web applications and login pages. It’s also why the information technology industry as a whole is working toward a universal specification for authentication to secure all accounts across the Web.
If your business website or your client’s site has ever been hacked, then you’ve experienced that sick feeling when navigating to the site only to discover a blue screen or receiving a notice from your host that the website has been suspended for suspicious activity. I know because it happened to me!
Unless you’ve had a professional security team audit your website, chances are it’s susceptible to a number of hacks.
According to the Open Web Application Security Project (OWASP), the Top 3 most common website vulnerabilities include:
- Injection – These occur when Web apps send user input and other untrusted data to a back-end server, such as a SQL database. Attackers can exploit these bugs to steal passwords or other sensitive table data. These breeches can also carry out denial of access attacks or, in some instances, take over the underlying Web server completely.
- Cross-site scripting – These bugs happen when Web apps send information supplied by the user to a browser without properly validating it. Attackers then steal browser cookies used to authenticate an end user to an e-mail account or other restricted service.
- Broken authentication and session management – These errors reside in apps used to log users in to restricted parts of a site where some sort of critical error occurs, such as requiring a session ID that is easy to guess or included in the URL. This allows attackers to take unauthorized control of user accounts and perform any action the valid user would, including deleting sensitive e-mail or personal information.
The above list is an abbreviated version of top threats, but I hope it provides enough incentive to take website security seriously. You can read an excellent overview, one written in layman’s terms, of the OWASP’s Top 10 threats at the ArsTechnica website, which also offers ways to combat these threats.
If you haven’t brought up the topic of website security with your clients yet, this may be the time to do so. Being proactive to secure the safety of your client’s business will go a long way in securing your client’s trust in you too!
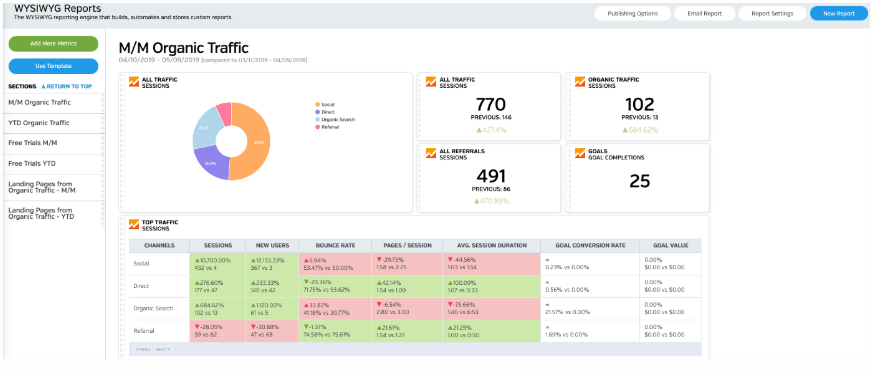
White Labeled and Branded Reports. Drag and Drop Editor. Automate your SEO, PPC, Social, Email, and Call Tracking Reporting.


Nice post. Will raven be updating its content manager, blog manager feature to work and integrate better with HTTPS instead of just HTTP?
It’s a known issue and we’ll be addressing it in the future, but not immediately.
Interesting you guys write a post about its importance yet not plan to support in an reasonable timeframe. Newsjack?
I can count on my hand the number of requests we’ve had to support SSL with our Blog Manager over the years. However, if Google’s new stance on SSL creates a strong demand for this in Raven, we’ll definitely shift our development priorities to getting SSL to work with the Blog Manager sooner than later.
As for newsjacking, I’m not sure this post counts as that 😉 But speaking of newsjacking, my buddy wrote an awesome book on it http://www.amazon.com/Newsjacking-Grant-Hunter/dp/0500516723/
Sounds great! And FWIW I think the SSL requirement is ridiculous for the vast majority of sites.
Not every site needs https, but it’s getting very close. It’s not just ecommerce, if it is social connected that may be enough of a reason.
Hi Kyle,
I’m inclined to agree. Search Engine Land this morning explained that Google is treating HTTPS on a per-URL page basis. Read more here: http://raven.im/VmkiVS